infosec
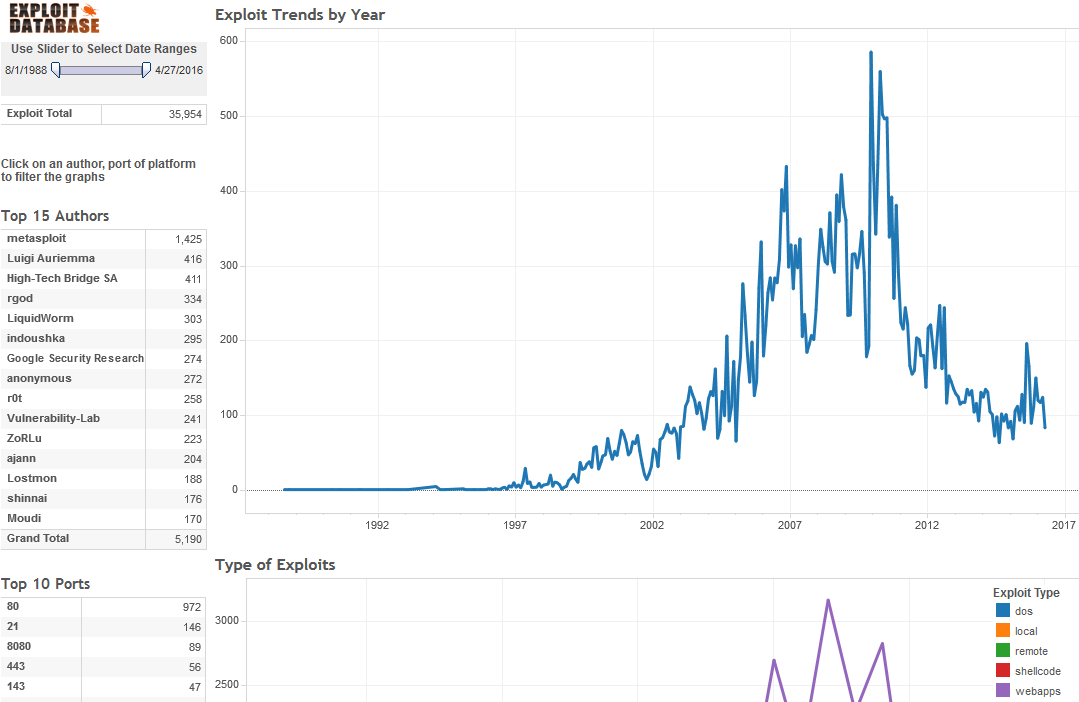
Computer Exploit Database Visualized
The ultimate archive of public exploits to corresponding vulnerable software; developed by penetration testers and vulnerability.
Privacy and Infosec Working Together
As new information security technologies are created, organizations need to assess their impact on privacy policy.
Information Management Risk Assessment
An information management program is simply a tool that provides a framework for making well-reasoned decisions regarding the company's processing of personal information.
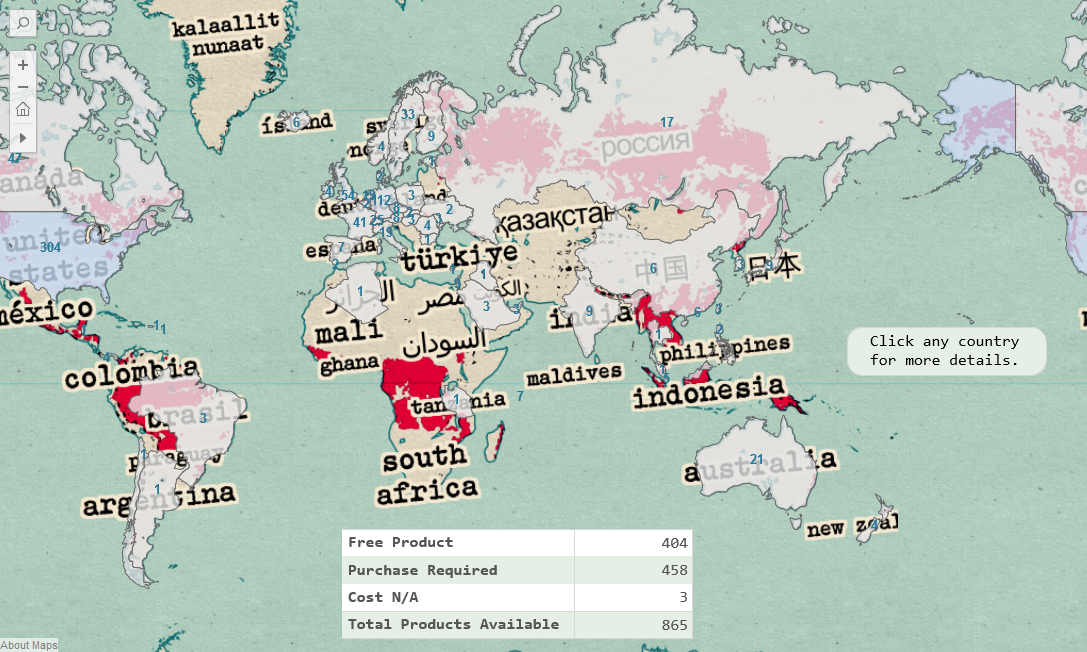
Tableau: Worldwide Encryption Products
The largest database of encryption products available around the world.
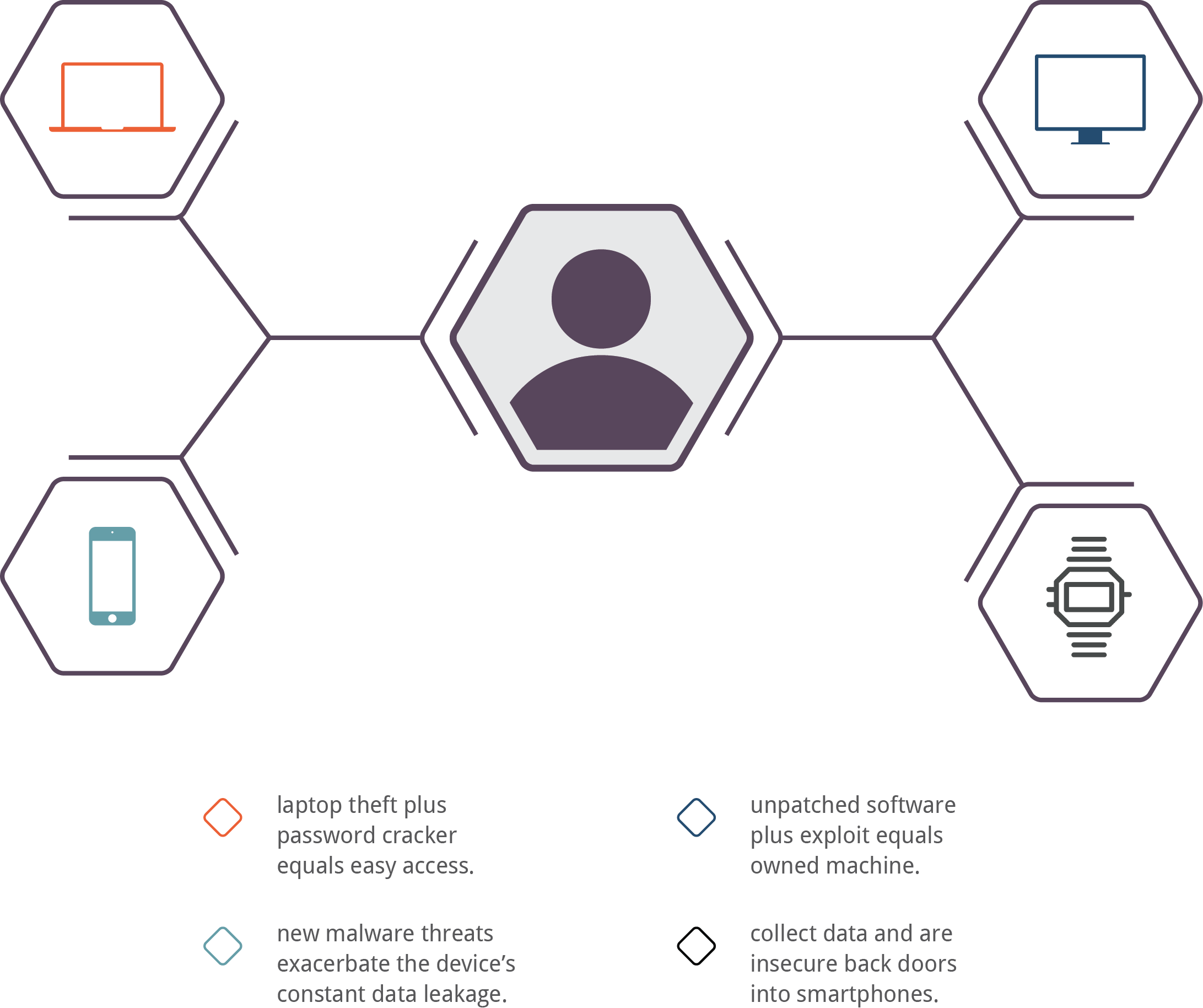
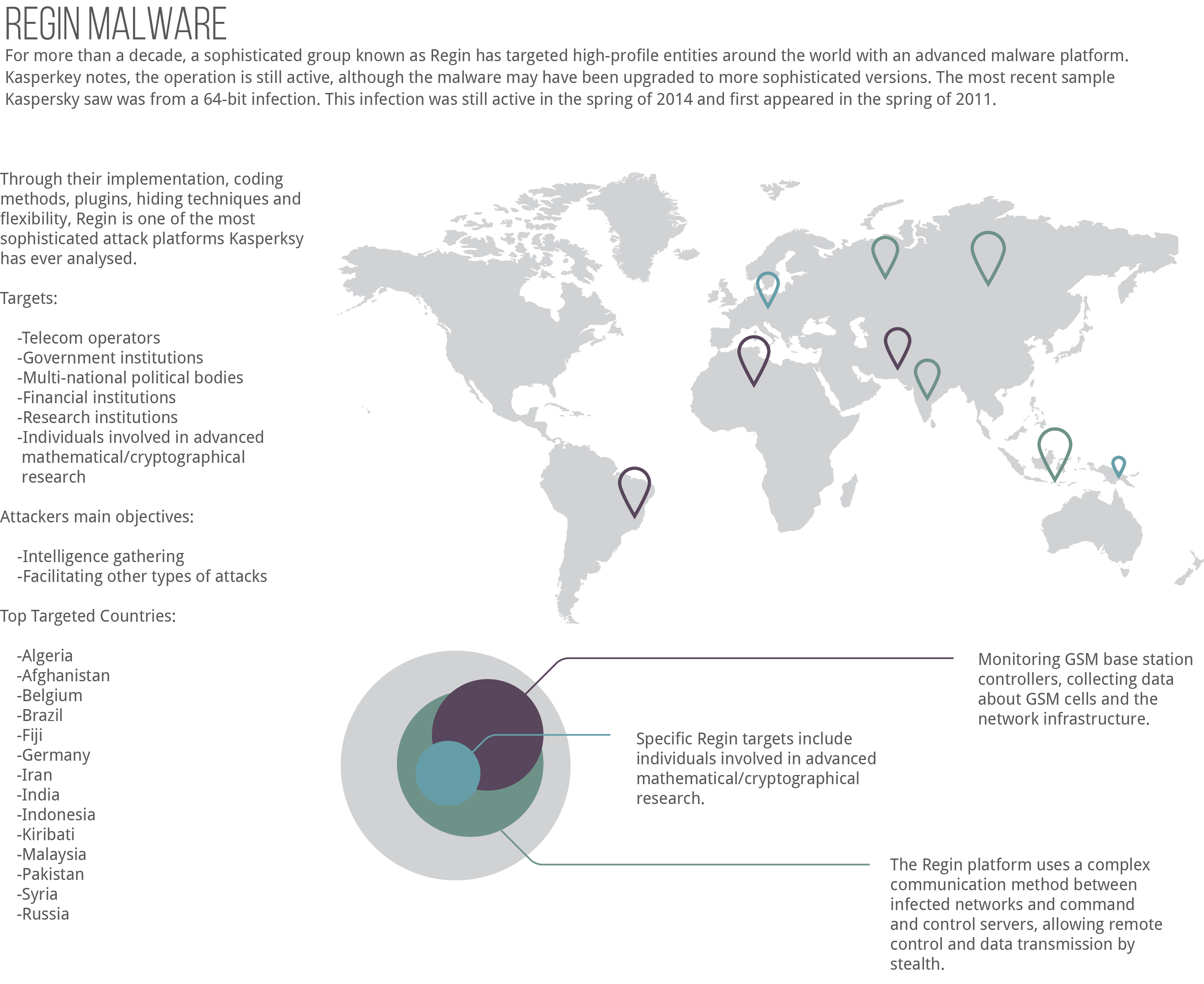
Regin Malware Infographic
Through their implementation, coding methods, plugins, hiding techniques and flexibility, Regin is one of the most sophisticated attack platforms Kasperksy has ever analysed.
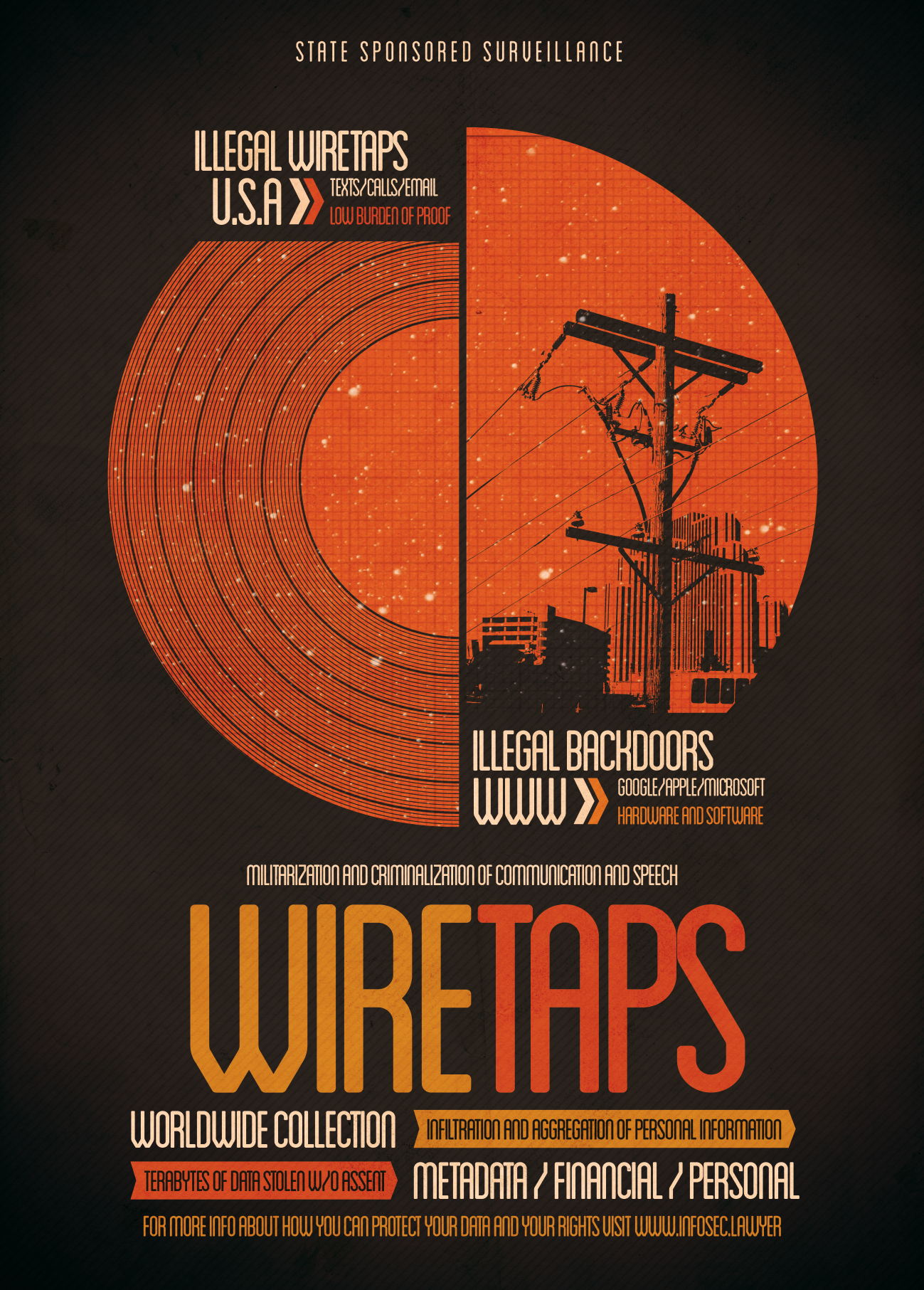
Wiretap and Surveillance Poster
propaganda poster highlighting illegal and legal state sponsored wiretapping and surveillance.
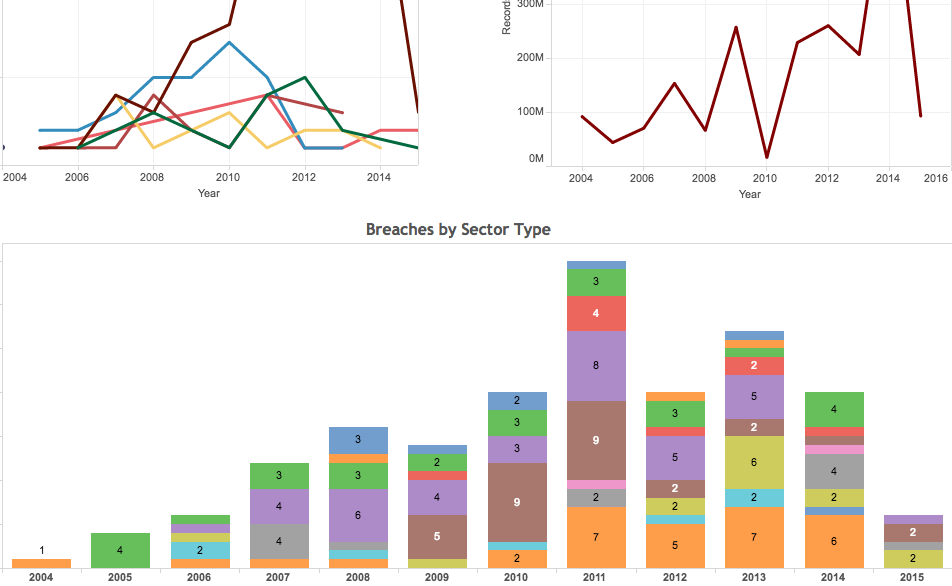
Tableau Interactive: Significant Data Breaches from 2004 to Jan 2015
This interactive data visualization examines significant data breaches since 2004.
Tableau Interactive: All HIPAA Data Breaches since 2009
Data Breaches in U.S. Affecting 500 or More Individuals (2009-2015)
Protect Your Privacy Poster
Our data is constantly being tracked, surveilled, sold, stolen, and compromised. We would be concerned if someone we didn't know had VHS tapes of our movements, yet we freely give away our location, data, and personal information. Governments, corporations and unsavory characters compile our data into profiles - they have tapes and tapes of information on us. Protect your privacy.
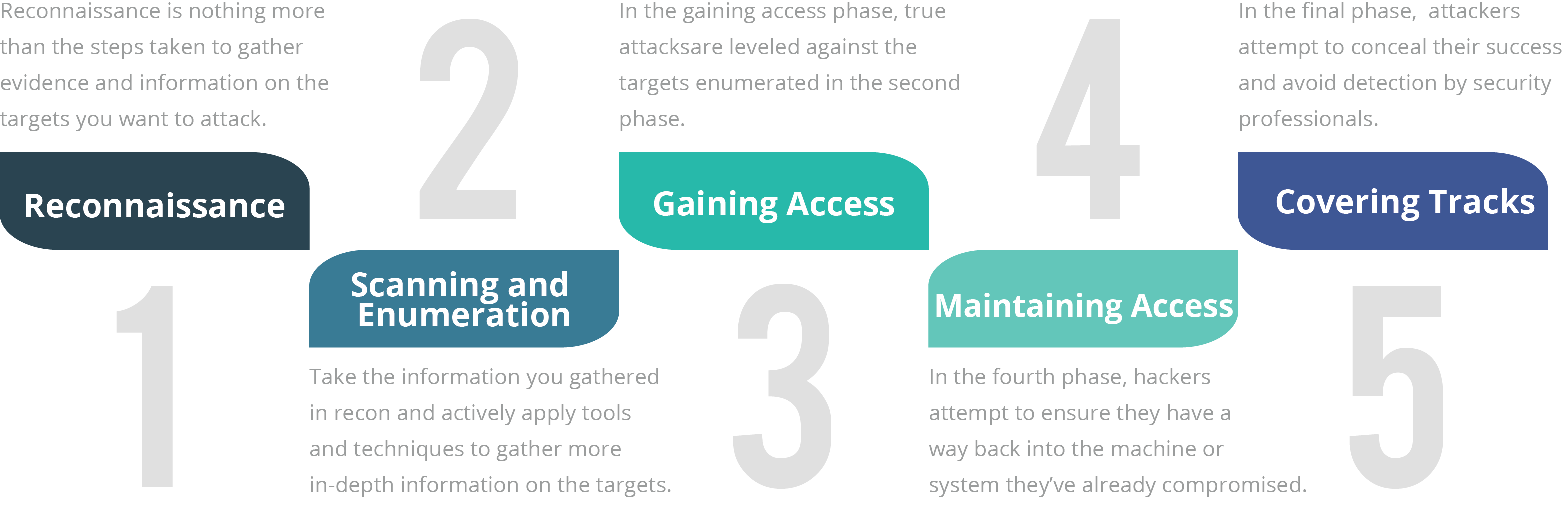
Ethical Hacking Phases
Although there are many different terms for these phases and some of them run concurrently and continuously throughout a test, EC-Council has defined the standard hack as having five phases. Whether the attacker is ethical or malicious, these five phases capture the full breadth of the attack.
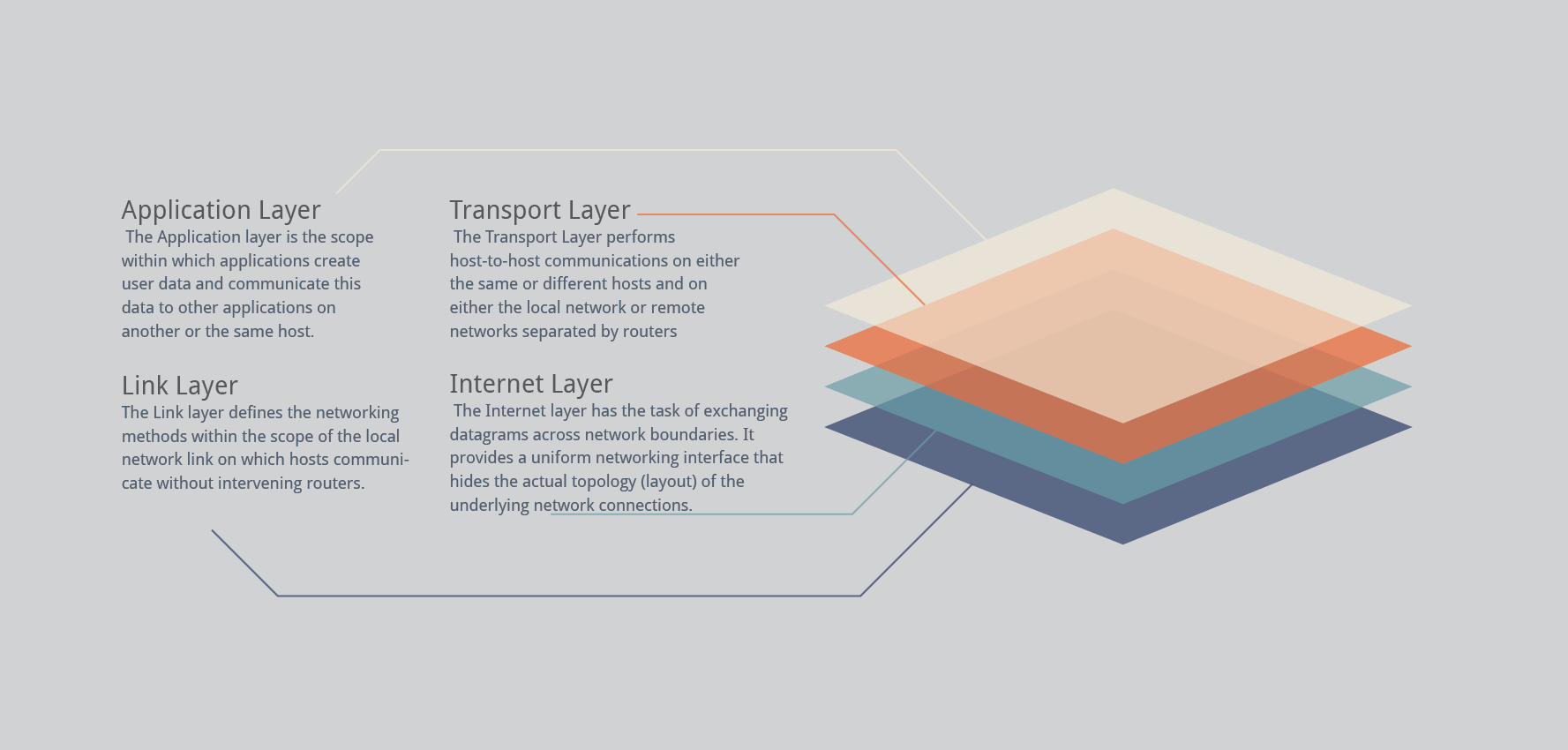
TCP/IP Protocol Suite
TCP/IP (transmission control protocol/Internet protocol) is the suite of communications protocols that is used to connect hosts on the Internet and on most other computer networks as well. It is also referred to as the TCP/IP protocol suite and the Internet protocol suite.